Overview
Why to use ByteCode-viewer for malware analysis? Bytecode viewer is a decompiler whose most relevant feature for malware analysis is the ability to decompile using six different decompilers. In addition, the bytecode viewer is also able to compile and edit code.
When to use ByteCode-Viewer ?
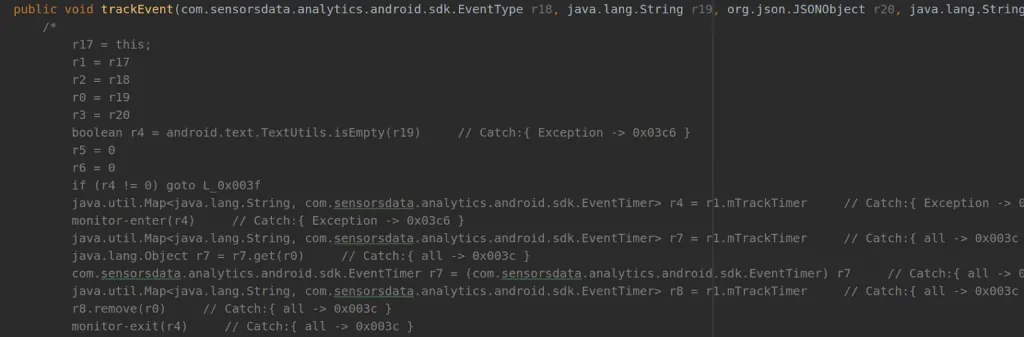
As we all know every standalone decompiler fails to decompile the whole code properly, as you can see in the picture below.
In these cases we can try and see the missing parts in Bytecode viewer, thanks to its ability to decompile in six different decompilers.
How to Use for Malware Analysis?
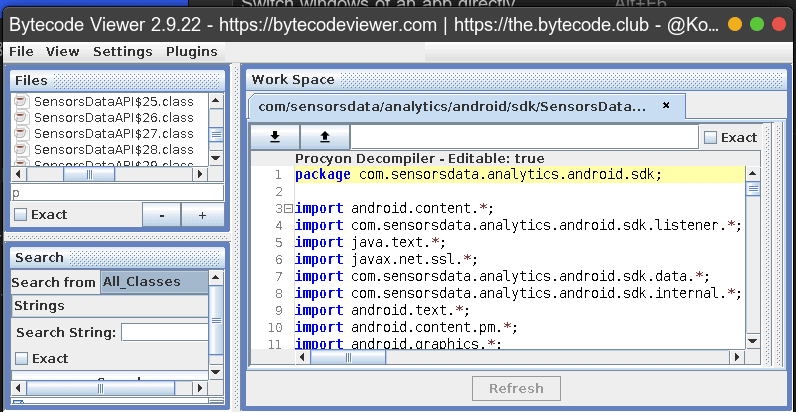
- Download the latest version from https://github.com/konloch/bytecode-viewer/releases and run the Bytecode-Viewer-2.9.x.jar. You may need to execute it via command line java -jar Bytecode-Viewer-2.9.x.jar (replace the X with the current minor version).
- Press the file tab → add → browse for your apk file.
- Prass the “view” tab and choose for each pane which decompiler to use by checking the box ”java” in the relevant decompiler. To apply your changes press the “refresh” button.
get in touch
Want to Hear More?
Write your Email here, we won't send any spam!
A free consulting meeting included.
A free consulting meeting included.